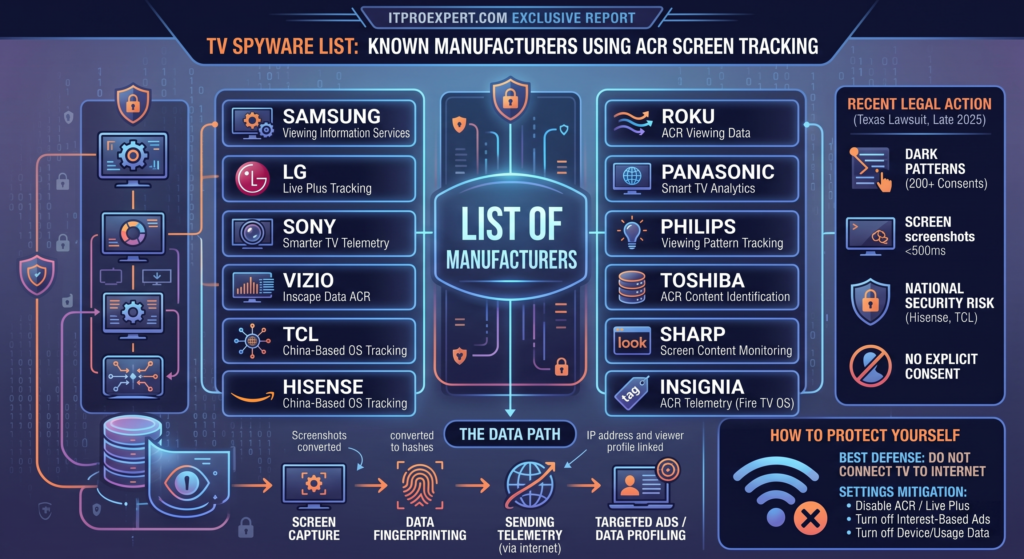
In the modern smart home or office, the television has evolved from a passive broadcasting screen into an active surveillance device. While consumers are distracted by 4K resolutions and bezel-less displays, major manufacturers—including Samsung, LG, Sony, and budget-friendly alternatives like Amazon’s Fire TV stick—have integrated highly aggressive tracking technologies directly into their operating systems.
Do you use a TV for corporate presentations – It could very well be leaking company secrets to another country.
This isn’t just about targeted advertising anymore; it’s about unauthorized screen capturing, deliberate code obfuscation, and national security risks. Here is the unvarnished truth about Automatic Content Recognition (ACR) and what hardware hackers have uncovered about your living room display. Even with the deepest attempts to see all the spy operations these TVs are capable of, it may never be know due to extreme obfuscation.
We have been shocked to capture the data flow from some of these TVs to see extremely personal information being sent internationally. Unbelievably you actually agreed to this when buying the TV but didn’t read the fine print. Even if you don’t use the built in TV app, it screen captures any HDMI input (Computer, Apple TV, Xbox, Laptop, PC, etc..) and sends the screen data to advertising and data brokers – literally 100’s of them. This includes your personal (via mic) audio in your home or corporate office even when not using the TV.
Brands you thought you could trust:
- Samsung
- LG
- Sony
- Vizio
- TCL
- Hisense
- Amazon
- Roku
- Panasonic
- Philips
- Toshiba
- Sharp
- Insignia
- Almost all TV Sticks
The Glass-Level Threat: What is ACR?
Automatic Content Recognition (ACR) is a technology embedded into the core operating system of almost every modern smart TV. Unlike traditional tracking that simply monitors which apps you open, ACR operates at the “glass level.” It intercepts the visual and audio data right before it is pushed to the physical screen.
Because it operates at this final stage, ACR is completely agnostic to the source. It effectively bypasses HDCP encryption on HDMI cables. Whether you are watching a built-in Netflix app, playing a video game on a Xbox/PlayStation, or casting private emails from a laptop connected via HDMI, the ACR system can see it all.
Instead of sending massive video files over the internet, the TV’s internal processor takes localized snapshots or samples of pixels and audio. It then converts these samples into compressed cryptographic hashes (digital fingerprints) and sends them to remote servers to match against vast databases, determining exactly what is playing on your screen down to the second.
The Screenshot Revelation and the DRM Irony
For years, the exact mechanism of this tracking was obscured. However, a 2024 peer-reviewed study by computer scientists at UC Davis, UCL, and UC3M confirmed that ACR technology actively captures full snapshots of the user’s screen.
The frequency of these captures is staggering:
- LG Televisions: The study found that LG devices capture on-screen data as often as every 15 seconds.
- Samsung Televisions: Captures occur approximately every 60 seconds.
- Extreme Cases: Legal investigations have alleged that some manufacturers’ systems are capable of taking screenshots as rapidly as every 500 milliseconds.
Independent developers reverse-engineering Android TV source code have also pointed out a frustrating double standard. The operating system explicitly uses Digital Rights Management (DRM) to disable a user’s ability to take a screenshot of protected video surfaces (like Disney+). Yet, the TV’s internal ACR system is granted the deepest system-level access to capture and hash that exact same content for their own corporate databases.
Hardware Hacks and Code Obfuscation
The cybersecurity community has been digging deep into how manufacturers hide these practices. Researchers attempting to reverse engineer the operating systems on Samsung and LG TVs found that the companies actively employ deliberate code obfuscation. They “strip” the firmware binaries (such as Samsung’s exeDSP file) of thousands of function names and symbols. This creates a labyrinth designed specifically to obstruct security researchers from understanding how the telemetry mechanisms operate under the hood.
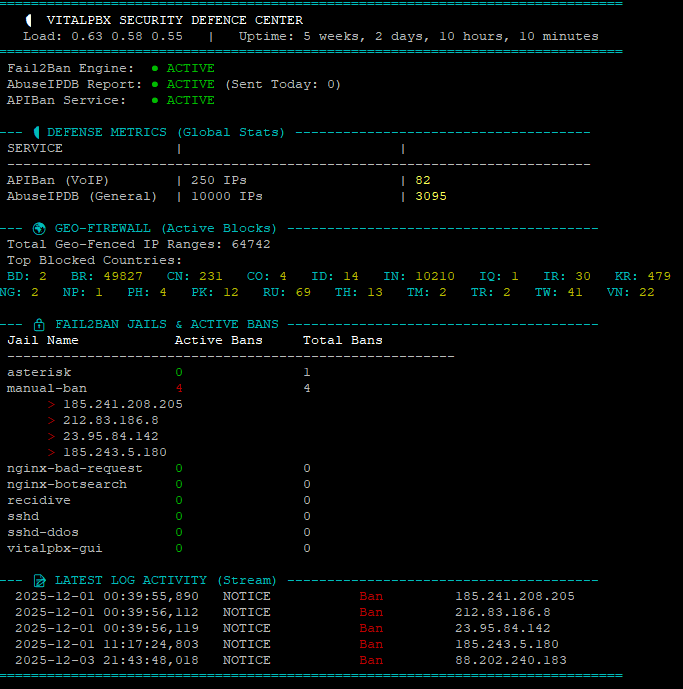
When software analysis isn’t enough, researchers have turned to hardware. Security groups like WithSecure Labs have physically bypassed TV software security by desoldering the eMMC memory chips directly from Samsung TV motherboards. By dumping the memory directly, they have uncovered hidden UPnP services, mapped out the internal memory structure, and exposed vulnerabilities that could allow malicious actors to use the TV as a backdoor into a home network.
Regional Tracking and The UK Context
By building custom “smart crawlers” to intercept network traffic, researchers found that tracking is practically unavoidable—with known trackers present on 89% of Amazon Fire TV apps. Interestingly, network audits reveal that for consumers here in the UK, the tracking actually behaves differently than in the US. Telemetry systems dynamically alter their tracking aggression and data collection methods based on regional IP addresses, adjusting just enough to stay within the bounds of local privacy regulations like the GDPR.
The Legal Backlash: Texas Lawsuit and National Security
In late 2025, the Texas Attorney General launched a massive lawsuit against five major TV manufacturers: Samsung, LG, Sony, Hisense, and TCL. The lawsuit alleges deceptive trade practices, pointing out that consumers must often navigate through more than 200 separate screens of legal jargon just to understand the tracking they opted into with a single click during setup.
The lawsuit also highlights a chilling national security risk. Hisense and TCL are massive players in the budget TV market and are owned by Chinese corporate entities. Legal filings note that consumer data collected by these brands could be subject to China’s National Security Law, which compulsorily requires Chinese companies to hand over collected data to the Chinese government if requested.
The Budget Trap: Amazon Fire TVs and Streaming Sticks
Buying a “dumb” monitor and plugging in a cheap streaming stick will not automatically save you from surveillance. Amazon Fire TVs and plug-in Fire TV Sticks natively run their own ACR protocols. Enabled by default during setup, these devices monitor your viewing habits to feed Amazon’s massive advertising network. Because Fire OS is also licensed out to third-party manufacturers, you might be buying a TCL or Hisense TV that is tracking you on behalf of the manufacturer and Amazon simultaneously.
How to Protect Your Network
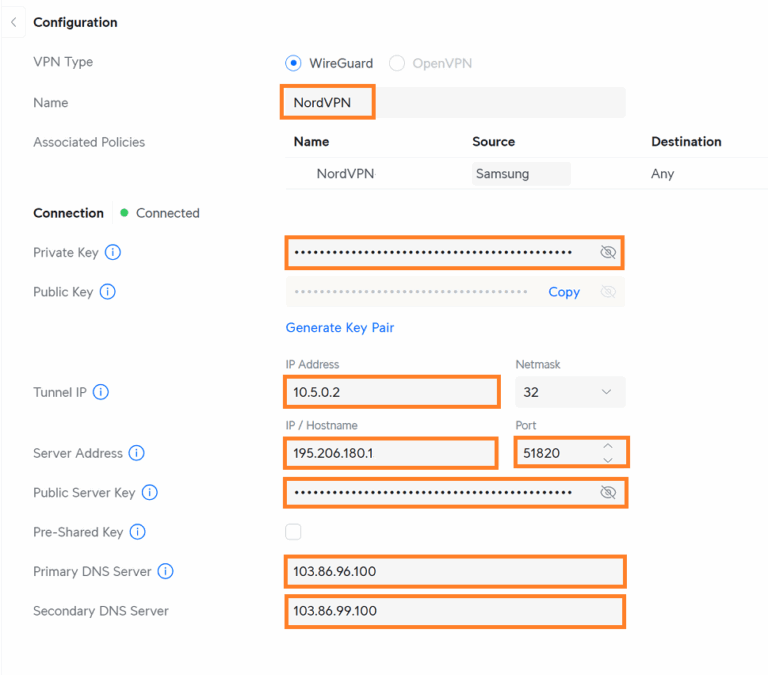
As an IT professional or a privacy-conscious consumer, the best way to secure a smart TV is to never connect it to the internet. Opting to use a dedicated, privacy-respecting streaming box (like an Apple TV) on a disconnected display is the gold standard.
If your TV must be online, dive into the settings immediately:
- Samsung: Go to Settings > Support > Terms & Privacy. Turn off ‘Viewing Information Services’ (ACR) and ‘Interest-Based Advertisements’.
- LG: Go to Settings > General > Additional Settings > General > Live Plus. Turn off ‘Live Plus’.
- Amazon Fire TV: Go to Settings > Preferences > Privacy Settings. Disable ‘Device Usage Data’, ‘Collect App Usage Data’, and ‘Automatic Content Recognition’.
Although those may not be enough in reality – Short of not connecting to WiFi or Cable – Use a UniFi Gateway Router, set the TV on a static IP and BLOCK its access to the internet completely.
The era of the passive television is over. Until stronger privacy legislation is enacted, the burden of protecting the living room falls entirely on the consumer. Its unbelievable that this type of literally white collar spyware is legal.