Notepad Plus Plus – Update Infrastructure Compromised by State-Sponsored “Lotus Blossom” Spies.
Download the Latest Chrysalis Backdoor Detection Software
3rd February, 2026 – updated 5th February
Major Detection Software Update 5th February 2026
New Findings Spark Additional Detection Protocols
Link to Notepad++ Lotus Blossom Chrysalis Backdoor IOC RAT Malware Detection Software
BREAKING: Notepad++ Espionage Campaign Expands with New “Sagerunex” Backdoor & Antivirus Abuse
Updated: 5th February, 2026
A sophisticated cyber-espionage campaign targeting users of the popular text editor Notepad++ has escalated significantly. Security researchers have confirmed that the Advanced Persistent Threat (APT) group known as Lotus Blossom (also tracked as Billbug or Spring Dragon) has not only compromised the software’s update mechanism but is now deploying a second, more dangerous backdoor known as “Sagerunex.”
This campaign, which has been active for nearly six months, allows attackers to selectively intercept traffic and push malicious updates to high-value targets in government, telecommunications, and critical infrastructure sectors.
The “Chrysalis” & “Sagerunex” Backdoors
The attack relies on a technique called DLL Sideloading to trick the operating system into running malicious code. While initial reports focused on the abuse of a Bitdefender binary, new intelligence confirms the group is also exploiting a legitimate Trend Micro debugging tool (tmdbglog.exe) to load their malware.+1
Victims who believed they were downloading a standard security update instead received a malicious NSIS installer. Once executed, this installer drops a hidden payload that performs two critical actions:
- Deploys Chrysalis: A custom backdoor hidden inside a modified DLL (
log.dllortmdglog.dll). - Installs Sagerunex: An advanced, memory-resident backdoor that mimics legitimate Windows services. It utilizes Microsoft Warbird—a complex code obfuscation technology—to hide its execution flow.
Unlike typical malware, the new Sagerunex variants tunnel their traffic through legitimate cloud services like Dropbox and Twitter (X), making the Command & Control (C2) traffic indistinguishable from normal user activity.
Timeline of the Breach
The compromise was not a momentary glitch but a sustained operation. Forensic analysis has established the following timeline:
- June 2025: Attackers gain initial access to the Notepad++ hosting provider’s infrastructure.
- June – September 2025: “Active Infection Phase.” Attackers redirect specific users to malicious servers.
- September 2, 2025: Hosting provider performs a kernel update, temporarily severing access.
- September – December 2, 2025: “Persistence Phase.” Attackers use stolen credentials and the Sagerunex backdoor to maintain access.
- February 2026: Full details of the new Trend Micro sideloading technique and cloud-based C2 infrastructure are made public.
What To Do If You Suspect Compromise
Because “Sagerunex” and “Chrysalis” are designed for long-term persistence, simple deletion of files is not enough. The malware utilizes advanced evasion techniques, including “Timestomping” (altering file creation dates) to blend in.
If you detect indicators of this malware on your network:
- Isolate the machine immediately. Disconnect it from the network.
- Assume Identity Compromise. The attackers utilize tools like ChromeKatz to harvest saved browser passwords. Reset all credentials used on that device.
- Wipe and Re-image. Do not attempt to “clean” the infection. A full format and OS re-installation is the only safe remediation.
New Detection Tool Available (Re-scan using new tool after 5th Feb)
Given the complexity of these backdoors, we have updated our specialized Lotus Blossom IOC Detector to version 1.4.
This standalone tool is designed to hunt for the specific artifacts dropped by this campaign, including the newly discovered Trend Micro variants. It performs a four-tiered scan:
- Deep File System Scan: Recursively checks for specific sideloaded DLLs and Warbird-protected loaders.
- Registry Analysis: Scans for malicious persistence keys that survive reboots.
- Network Telemetry: Analyzes active connections for communication with known C2 nodes (e.g.,
45.76.155.202). - Recon File Check: Looks for hidden temporary files (
VT001.tmp) used by the malware to store stolen system data.
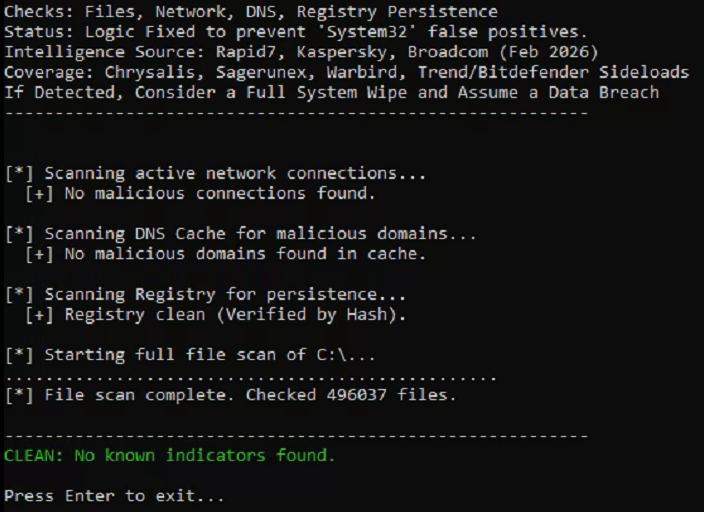
Important Usage Instructions: Download, UNZIP to a new folder, then right-click the detector and run as ‘Administrator’. (Note: This tool requires Administrator privileges to access protected system directories and network tables.)
Our software is certified (Ravtic LLC code signed) – safe, secure, private, and free to use. All code runs locally on your system.
Detailed Technical Breakdown
Below are the specific indicators the software detects. A match on both name and hash confirms a compromised system.
1. File System Artifacts (Malware Payload)
The tool scans the C: drive for these specific filenames.
Group A: Initial Infection (The Dropper)
- update.exe
- Description: The malicious NSIS installer mimicking a Notepad++ update.
- Hash:
a511be5164dc1122fb5a7daa3eef9467e43d8458425b15a640235796006590c9
Group B: The Chrysalis Backdoor (Bitdefender Variant)
- BluetoothService.exe
- Description: A legitimate Bitdefender binary renamed and abused to side-load the malicious DLL.
- Hash:
2da00de67720f5f13b17e9d985fe70f10f153da60c9ab1086fe58f069a156924
- log.dll
- Description: The actual Chrysalis malware loaded by the Bitdefender binary.
- Hash:
3bdc4c0637591533f1d4198a72a33426c01f69bd2e15ceee547866f65e26b7ad
Group C: The Chrysalis Backdoor (Trend Micro Variant) — NEW
- tmdbglog.exe
- Description: Legitimate Trend Micro debugging tool abused for sideloading.
- Hash:
f9036b967aaadf51fe0a7017c87086c7839be73efabb234e2c21885a6840343e
- tmdglog.dll
- Description: Malicious DLL loaded by the Trend Micro executable.
- Hash:
b75a161caab0a90ef5ce57b889534b5809af3ce2f566af79da9184eaa41135bd
Group D: Loaders & Evasion Variants
- ConsoleApplication2.exe
- Description: Specialized loader using Microsoft Warbird obfuscation.
- Hash:
b4169a831292e245ebdffedd5820584d73b129411546e7d3eccf4663d5fc5be3
- loader1 / loader2
- Description: Variant loaders found in public repositories.
- Hash:
0a9b8df968df41920b6ff07785cbfebe8bda29e6b512c94a3b2a83d10014d2fd(Loader 1)
Group E: Tools & Clean-up
- u.bat
- Description: Batch script used by the malware to delete itself.
- Hash:
9276594e73cda1c69b7d265b3f08dc8fa84bf2d6599086b9acc0bb3745146600
- datechanger.exe
- Description: “Timestomping” tool used to alter file creation dates to hide tracks.
- Hash:
b337a3b55e9f6d72e22fe55aba4105805bb0cf121087a3f6c79850705593d904
2. Active Network Connections
The tool scans for active TCP connections to the following attacker infrastructure:
95.179.213.0(Malicious Update Host)61.4.102.97(C2 Server – Malaysia)45.76.155.202(NEW – C2 Server)51.91.79.17(NEW – C2 Server)
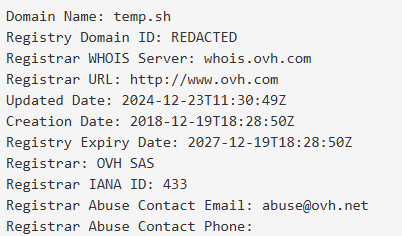
3. DNS Cache History
The tool checks if the machine has previously resolved these domains:
api.skycloudcenter.com(Primary C2)api.wiresguard.com(Cobalt Strike Beacon)temp.sh(NEW – Exfiltration Site)