In 2026 AI is really starting to hit companies hard, 2025 was a cake walk in comparison. AI can now find vulnerabilities in any software or online service. Attacks are now sophisticated intelligent fraud & phishing operations with AI leading the way, giving ransomware a run for its money.
If you have not already thought about locking down your business cyber security, now is literally the time.
“Cyber-enabled fraud has displaced ransomware as the #1 concern for CEOs. In a major shift from 2025, fraud and phishing now dominate in 2026 — driven by AI-powered impersonation, deepfake voice and video attacks, and highly targeted social engineering at scale (especially via email). 73% of respondents were personally affected in 2025.” – Everyone says: “nobody will bother with me” or “I have nothing to loose” – until it actually happens and only then do you realise what was actually important, how far legal pursuits from other companies can go and remediation costs/fines that could wipe your company out. If you have cyber insurance, you actually need to be implementing a strong level of protection otherwise they may not pay out and the bill can be in the tens to hundreds of thousands.
In 2025 a cyber attack risk to any size company was about 5 to 18% and now in 2026 it is over 43%.
Global Cybersecurity
Outlook 2026
Cybersecurity in 2026 is accelerating under three compounding forces: the dual-use explosion of artificial intelligence, deepening geopolitical fragmentation, and a widening gap between well-resourced and under-resourced organisations. This report distils the most critical data and insights from the WEF Global Cybersecurity Outlook 2026 for IT and business leaders.
01 AI Is Supercharging the Cyber Arms Race
Artificial intelligence has become the defining technology on both sides of the cybersecurity battle. Defenders are using it to detect intrusions, automate threat response and process vast security telemetry. Attackers are leveraging it for hyper-personalised phishing, automated vulnerability discovery and deepfake-powered social engineering — creating a faster, more unpredictable threat landscape that traditional frameworks cannot keep pace with.
AI Adoption for Cyber Defence
77% of organisations have now deployed AI-enabled security tools — primarily for phishing detection (52%), intrusion and anomaly response (46%) and automated security operations (43%). Yet roughly one-third still have no process to validate AI security before deployment.
Top Concerns About Generative AI (2026 vs 2025)
Notable shift: in 2025, adversarial capability advancement topped this list at 47%. By 2026, data leaks have overtaken it — signalling that unintended data exposure is now the primary concern.
“Criminals are always willing to use all possible ways to get access to value. To stay ahead, those of us who defend must use every tool at our disposal — which now includes agentic AI.”
— Arvind Krishna, CEO, IBM02 Geopolitics: A Defining Force in Cyber Risk
Geopolitics remains the single largest factor shaping organisational cyber risk strategies in 2026. Nation-state attacks on critical infrastructure, escalating hybrid warfare, and the fracturing of global technology supply chains are forcing businesses to fundamentally rethink their risk posture. A Norwegian hydropower dam was hacked in April 2025, opening floodgates releasing 500 litres of water per second for four hours. Telecommunications networks in the United States were penetrated by advanced nation-state actors. These are no longer edge cases.
Regional Confidence in National Cyber Preparedness
% of respondents confident their country can respond to critical infrastructure attacks
- Middle East & North Africa84%
- North America47%
- East Asia & Pacific40%
- Europe & Central Asia40%
- South Asia38%
- Sub-Saharan Africa37%
- Latin America & Caribbean13%
Public Sector Lagging on Cyber Resilience
While 11% of private sector organisations report insufficient cyber resilience, the figure nearly doubles to 23% for public sector and international organisations — despite being the primary target of state-sponsored espionage and infrastructure attacks.
03 Cyber-Enabled Fraud Is Now Everyone’s Problem
Cyber-enabled fraud has displaced ransomware as the #1 concern for CEOs. In a major shift from 2025, fraud and phishing now dominate — driven by AI-powered impersonation, deepfake voice and video attacks, and highly targeted social engineering at scale. 73% of respondents were personally affected in 2025.
04 The Boardroom–Frontline Divide
A significant divergence has emerged between how CEOs and CISOs prioritise cyber risk. CEOs have pivoted sharply towards fraud and AI threats, focused on financial exposure. CISOs remain anchored on ransomware and supply chain resilience, managing day-to-day operations. Both views are valid — but the gap between them is itself a governance risk.
| Rank | CEO Top Concerns (2026) | CISO Top Concerns (2026) |
|---|---|---|
| 1 | Cyber-Enabled Fraud & Phishing | Ransomware Attack |
| 2 | AI Vulnerabilities | Supply Chain Disruption |
| 3 | Exploitation of Software Vulnerabilities | Exploitation of Software Vulnerabilities |
Among CEOs of highly resilient organisations, AI vulnerabilities rise to the very top of the concern list — suggesting that a mature security posture sharpens visibility of the emerging AI threat horizon.
05 Supply Chain: The Widening Attack Surface
The rush to reconfigure global supply chains — driven by trade tariffs, export restrictions and geopolitical realignment — is expanding the attack surface faster than security controls can follow. Organisations are establishing alternative suppliers and data-hosting arrangements, often outpacing cyber due diligence in the process.
How Resilient Organisations Manage Supply Chain Risk
Figures represent highly cyber-resilient organisations. Less resilient organisations report these practices at just 6–31%.
06 Cyber Inequity: A Growing Global Divide
The gap between cyber-resilient and cyber-vulnerable organisations continues to widen. Skills shortages and funding constraints are most acute outside Europe and North America, creating a two-tier cyber world where the organisations most frequently targeted are often the least equipped to defend themselves.
07 Key Takeaways for IT & Security Leaders
🛡 Govern AI Before It Governs You
Nearly a third of organisations have no process to validate AI security before deployment. Prioritise AI security assessments, embed security-by-design into AI procurement, and mandate continuous — not one-time — validation for all AI-enabled tools.
🌐 Treat Geopolitics as a Cyber Trigger
Every geopolitical shift — trade tariffs, vendor changes, supply chain reshoring — must trigger fresh threat modelling and vendor-risk reassessment. Cyber risk management must operate in lockstep with geopolitical intelligence.
🎣 Fraud Is the New Ransomware
AI-powered social engineering, deepfake impersonation and invoice fraud now represent the fastest-growing financial cyber risk. Multi-factor verification for financial authorisations and executive awareness training are no longer optional.
🔗 Secure the Supply Chain Proactively
Integrate security into every procurement decision. Assess supplier cyber maturity, conduct joint incident simulations with key ecosystem partners, and map your third-party exposure in detail.
🤝 Collaboration Is a Security Control
The most cyber-resilient organisations invest in threat intelligence sharing, government engagement and cross-industry information-sharing groups. Lone-wolf security strategies are increasingly inadequate.
“Cybersecurity is the foundation for our digital world. It is at the heart of trust and will allow society to fully benefit from AI and quantum. But it’s not something one can do on their own. We have to come together, share intelligence globally and develop the skills equal to emerging risks.”
— Michael Miebach, CEO, Mastercard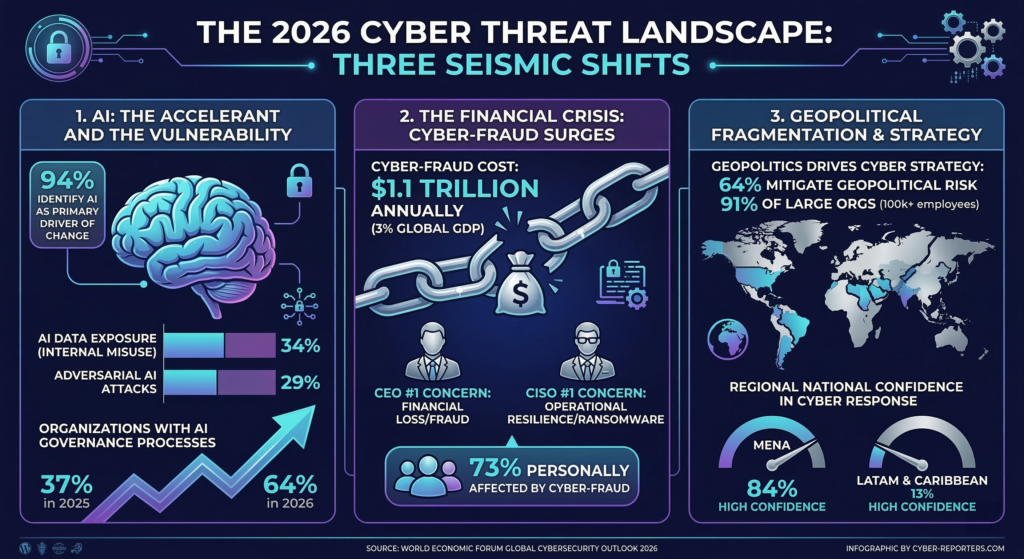
Read the detailed full report here : https://reports.weforum.org/docs/WEF_Global_Cybersecurity_Outlook_2026.pdf