2025/2026 IT & Security Policy for SME using MS365
This document may not be redistributed but can be used or modified for internal business use.
I. Access and Security: The First Line of Defence
The security of our company’s IT infrastructure relies on controlled access and empowered employees serving as our first line of defence. Failure to comply can result in legal action and significant costs to the company from regulatory fines, service fees, and intellectual property loss.
1. Account Structure & Identity
Unique Identity: Every user must have their own unique username and password. Shared accounts (e.g., “office@”, “admin@”) are strictly prohibited for individual use. Account Separation:
- Standard Users: All day-to-day business activities (email, web browsing, document creation) must be performed using a “Standard” user account.
- Administrator Accounts: Staff with administrative privileges must have a separate, dedicated account (e.g.,
admin_jdoe) used only for administrative tasks (installing software, system configuration). - Prohibition: You must never browse the web or check email while logged into an Administrator account.
- Adding Users: Staff may never add another staff member to a PC that has not been setup and authorised by IT for that specific user. It can result in security issues, incorrect application configuration, loss of data, misconfigured privileges, backup failures, access issues and more.
2. Securing Your Accounts: Passwords, Passkeys & 2FA
This policy applies to all accounts used for work, including internal company systems (e.g., Office 365, Windows Login) and any external websites or services. Your credentials are the primary key to company data, and securing them is your most critical responsibility.
If you fail to secure accounts with Passkeys/2FA/MFA, then you are failing the most important security measure there is.
Secure all email accounts first, then any site that you can purchase from and any financial related sites, then continue with the rest.
Absolutely never use the same password twice and make sure it is random as per the guidelines below.
A. Credential Strength & Uniqueness
- Passwords: Where used, passwords must be a minimum of 12 random characters, containing a mix of uppercase letters, lowercase letters, numbers, and symbols.
- Passkeys: Where available, using a Passkey is a preferred and highly secure alternative to a traditional password.
- Uniqueness: You must use a completely different, unique password or passkey for every single website and service. Reusing credentials, even for non-critical sites, is a serious security violation.
- Compromise: If you suspect your password has been compromised (e.g., you clicked a phishing link), you must change it immediately and notify IT.
B. Mandatory Two-Factor Authentication (2FA/MFA)
- 2FA/MFA (or a Passkey) must be enabled on all company systems and any external service that supports it (Microsoft 365, VPNs, Payroll systems, etc.).
- Once enabled, you must never disable, delete, or remove 2FA/MFA or its associated authenticator app from your mobile device.
- MFA Fatigue Warning: You must never approve an MFA prompt (app notification or SMS) that you did not initiate yourself. If you receive an unexpected prompt, report it to the IT Department immediately.
C. Secure Credential Management
- Approved Tools: To comply with these rules, all passwords must be generated, stored, and managed using one of two IT-approved methods:
- The Microsoft Edge browser’s password manager, synced to your 365 profile.
- An IT-sanctioned password manager, such as ProtonPass or 1Password.
- Prohibited Storage: Do not write passwords down on sticky notes, in unsecured files (e.g.,
passwords.docx), or use any unapproved storage method. - IT Recovery: When using an IT-sanctioned password manager like ProtonPass, you must set the IT Department as the emergency recovery contact.
- Your Responsibility: You are responsible for all activity conducted using your credentials. Passwords and 2FA codes must never be shared with anyone.
3. Lock Screens & Physical Security
Locking: You must lock your computer and mobile devices whenever you step away from your desk, even for a short period.
- How-to: On a Windows PC, press Windows Key + L or Ctrl + Alt + Del (select ‘Lock’).
- Auto-lock: It is also possible to set a screensaver to auto-lock after 2-5 minutes or a mobile device dynamic lock (walk away lock).
Clear Desk Policy: Sensitive documents and unlocked devices must not be left visible on desks when the workspace is vacant.
Vehicle Security: Devices left in vehicles must be locked in the boot (trunk) and not visible from the outside.
4. Report Lost or Stolen Devices Immediately
Any company-issued or personal device used for work that is lost or stolen must be reported to the IT Department immediately (within 2 hours) so a remote wipe command can be issued.
5. Beware of Phishing and Social Engineering
Please maintain heightened vigilance regarding unsolicited or known communications—including emails, text messages, and phone calls—that request sensitive information. If you encounter any suspicious activity, report it to the IT Department immediately.
Evolving Threats: AI Voice Cloning Be advised that threat actors are now utilizing advanced Artificial Intelligence to replicate human voices. These “deepfakes” can perfectly mimic a colleague’s speaking style and tone. Do not rely solely on voice recognition to verify a caller’s identity; always verify unusual requests through a secondary channel.
The “Human Firewall” and Financial Implications While our technical safeguards are robust, your critical thinking is our primary defense. Technical barriers cannot stop a user who unknowingly grants access to a bad actor. Please be aware of the significant consequences of negligence in this area:
- Investigation Costs: Cyber forensic investigations are not covered by standard IT support policies. Failure to adhere to security guidelines can result in direct departmental charges for investigation services.
- Operational Loss: This figure excludes potential liabilities arising from financial theft or the loss of intellectual property, which can be far more severe.
- According to IBM – The “Cost of a Data Breach Report” (2025), the average total cost of a data breach for a UK organization is approximately £3.29 million.
- This massive figure includes the investigation, plus legal fees, regulatory fines (GDPR), lost business, and PR crisis management.
| Severity of Breach | Scope of Investigation | Estimated Fee |
| Minor Incident | Analyzing a single compromised laptop or email account (BEC). | £2,500 – £6,000 |
| Medium Incident | Ransomware or breach affecting a server and multiple endpoints. Requires network analysis to find “Patient Zero.” | £15,000 – £45,000 |
| Major Incident | Full network compromise, data exfiltration verification, and regulatory reporting (ICO) assistance. | £60,000 – £150,000+ |
For an individual user, falling for a phishing email can result in:
- Theft of saved and typed passwords, including for email, banking, and social media.
- Exposure of confidential documents, photos, or other sensitive files taken straight from the system.
- Surveillance via periodic screenshots or, where configured, webcam capture.
- Use of the machine as a foothold to attack other devices on the same home or office network.
This in turn can lead to company wide infections using custom AI undetectable code or further infect people from your stolen contacts list being tricked by AI code that will exactly mimic a reply from your pre-existing email threads that will continue an existing conversation to ensure nothing is suspicious. This will now include a new phishing malware link designed to infect further people.
- Browser Practices: The designated and required search engine is Google which must be used with the Edge Browser (No other browsers are allowed). The browser must be synced to your 365 profile. You must be able to distinguish between a paid advertisement link and a natural search result. Never click on search result adverts, as they can be faked by attackers to redirect you to a malicious site.
- Browser Security Warnings: Do not bypass browser security warnings (e.g., “This site is unsafe”) to access a website.
- Browser Extensions: No browser extensions are permitted except for the single, IT-approved antivirus extension. This means no voucher, shopping, ad-blocking, grammar-helper, or any other extensions.
- Email Link and Attachment Safety: Do not click on links or open attachments in any email, even if it appears to be from another staff member, an accounts department, or the company owner.
- If an email/document/pdf prompts you to “log in” or paste a ‘code’ to view a document or a secure file —this is a major red flag.
- Always verify the request through a separate secured (Signal) communication channel before taking any action.
- Do not install any software of any kind, nor any remote support from any 3rd party company even if you know them.
- Executables: Some emails may block executable attachments (.exe, .vbs). Do not attempt to bypass this by renaming files. Nor run any files inside of a .zip/.rar type of compressed file.
- Unusual Requests (Financial Security): Do not action requests for money transfer, gift cards, unknown invoices, loans, vouchers or any other kind of payments that appear to come from other staff, the owner/director, or external suppliers.
AI allows for scammers to fake the voices of anybody easily, construct emails in the style of anyone and call using phone numbers you know.- Verbal Verification: You must obtaining confirmation in person or using an outbound trusted number via a secure method that cannot easily be faked like a regular voice call. Ideally use the ‘Signal app’ when setting up or amending any payee details or transferring funds, making payments or dealing with any sensitive data.
- No matter how much the caller or email says it is “urgent” or “confidential” or “I need a favour as I am sick/busy/meeting”. Don’t do it.
- Know how to tell the difference between an advert and a natural search result on a browser as this can easily lead to a safety breach.
- If you feel you are not IT literate, not up to date with AI abilities/usage or do not understand any of this, please ask your manager or the director to arrange training for you.
6. Secure Wi-Fi & Network Usage
- Public Wi-Fi: Public Wi-Fi networks (cafes, hotels, trains) must be treated as hostile and must not be used for accessing sensitive company data directly. When working remotely, you must use a secure, password-protected network or the company-provided Virtual Private Network (VPN). Do not use 3rd party VPNs.
- Home Security: Staff working from home must ensure their router is secured with a strong, unique admin password (not the default one printed on the sticker, if changeable) and has the latest firmware installed.
- Internal Wi-Fi: Internal office Wi-Fi passwords should never be shared. Use the designated Guest Wi-Fi network for any third-party access.
7. Principle of Least Privilege
Employees will only be granted access to the data and systems necessary for their job. If you find you have access to a system or data that you believe you should not, you must report this to the IT Department immediately.
II. Acceptable Use of Company Resources: Setting Clear Boundaries
This section defines how company-owned hardware, software, and internet access can be used to maintain productivity and prevent misuse.
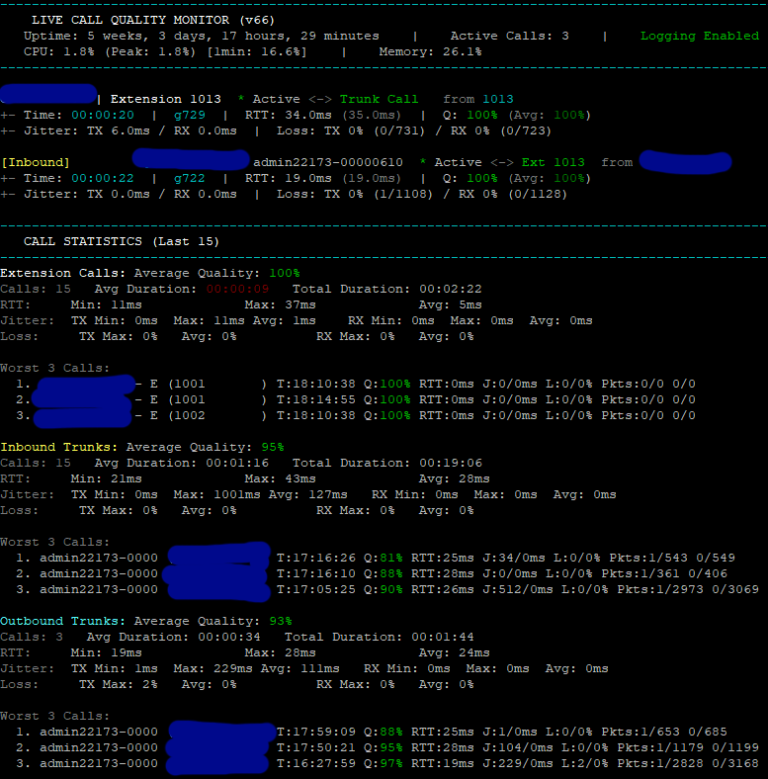
Notice of Monitoring: Please be advised that all company-provided resources and systems—including office computers, mobile phones, desk or portable phones, VoIP phones, VoIP apps, regular calls, and internet usage—are subject to monitoring. No personal calls should be made using business devices. This is done to ensure compliance with company policies, protect against security threats, and maintain system integrity. Employees should have no expectation of privacy when using company equipment or networks. (This is a legally accepted expectation in UK law).
8. Business Use is Priority
Company-provided IT resources are for business purposes. While minimal personal use may be acceptable, using company devices or accounts for significant personal activities (such as managing a personal business, extensive social media, or storing a large personal media library) is strictly prohibited.
9. Prohibition of Illegal Activities
Company resources must not be used for any illegal activities, including downloading copyrighted material, harassment, unauthorised VPN use, accessing gambling sites, or accessing inappropriate/explicit content of any kind.
10. No Unauthorized Software or System Changes
- Installation: You are prohibited from installing any software (including remote support), games, trialware, or browser add-ons without prior IT approval.
- Bloatware: You are prohibited from installing unnecessary software.
- Browsers: You are prohibited from installing alternative web browsers or changing the IT-configured default browser.
- SSO/Sign-up: You are not allowed to use your work credentials to grant access to or sign up for unauthorised third-party systems.
- Access: You are not allowed to sign into another person’s device, without pre-approval and pre-setup with IT support.
- Configuration: You are not allowed to configure your own laptop/PC from new.
- Auto-Play: The “Auto-Play” or “Auto-Run” feature for USB drives and CDs is disabled to prevent malware execution. Do not attempt to re-enable this.
- Firewalls: The software firewall (e.g., Windows Defender Firewall) must remain active on all network profiles (Domain, Private, and Public).
11. Off-Site Equipment Policy
When any company equipment (e.g., laptops, mobile phones, motor vehicles) is taken away from the work environment, the following rules apply:
- The equipment must be formally signed out.
- It must not be used by any third party, including family, friends, or children.
- No additional software may be installed, nor remote access granted, without explicit IT approval.
- It should only be kept off-site for the period that is absolutely necessary for your work.
- GPS tracking, where available, must be enabled and never disabled.
- Ownership and Responsibility: All equipment remains the property of the company. Failure to return equipment is considered theft and will be treated accordingly.
12. Responsible Internet and Application Usage
- Prohibited Content: Using any device on the company network to access, download, or distribute explicit, offensive, or objectionable material is strictly forbidden.
- Downloads: Do not download executable files (.exe, .msi, .bat) from websites or emails. Sometimes these can also include files that may contain links or can possibly infected in other ways, which surprisingly can be known files like: .doc, .docx, .xls, .xlsx, .vbs, .pdf type files.
- Productivity: Browsing social media sites, non-work-related websites, or using personal apps during work hours is prohibited, except during designated break times. This includes any deliberate time wasting tasks of any kind.
- Network Performance: Excessive personal internet usage that impacts network performance is not permitted.
13. Professional Digital Conduct
- Communications: All communications on company platforms must be professional and respectful.
- Social Media: Be mindful of your social media presence (text, video, or images). Do not post confidential company information, never post about any other staff member without their permission, and never post content that could damage the company’s reputation, as this may result in legal action.
14. Respect for Copyright and Intellectual Property
Unauthorized copying or distribution of copyrighted materials is prohibited.
III. Data Handling and Protection: Safeguarding a Critical Asset
Protecting company and customer data is a legal and ethical obligation.
15. Data Classification
You must be aware of the sensitivity of the data you handle and treat it accordingly.
16. Secure Data Storage
- Approved Storage: Sensitive data must only be stored on company-approved servers, cloud storage (e.g., OneDrive for Business, SharePoint), or encrypted devices.
- Prohibited Storage: Storing sensitive data on personal devices, personal cloud drives (e.g., Personal Dropbox, Google Drive, iCloud), unapproved services, or unencrypted USB sticks is strictly prohibited.
17. Data Encryption
All company laptops (that leave the business for any period) and mobile devices/USB drives that store or access sensitive data must be encrypted (e.g., BitLocker, FileVault).
18. Secure Data Transfer
- When sending sensitive data, you must use encrypted email or other secure transfer methods approved by IT.
- Personal Email: Do not email sensitive or business data to a personal email addresses.
- USB: Do not copy any company data to any USB or portable device. Also do not insert any USB device into any computer.
19. Proper Data Disposal
Printed documents with sensitive information must be shredded. Electronic files must be securely deleted.
20. Regular Data Backups
You are responsible for ensuring your critical work files are saved in designated network locations or specifically assigned drives (e.g., OneDrive, SharePoint) for regular backup by IT. Do not assume ‘Desktop’, ‘Music’, ‘Videos’, ‘C:\’ or any others folders are backed up. Ask if unsure. Do not save data to an external drive or USB stick (for both security and reliability reasons).
21. Prohibition of Unauthorized Data Sharing
Company data must not be shared with unauthorized individuals or external parties. This is a strict legal requirement.
22. Reporting Data Breaches & Incidents
It is the duty of every employee to report suspected security incidents immediately. You must report:
- Suspected phishing attacks or clicked links.
- Lost or stolen devices.
- Accidental data leaks (e.g., sending an email to the wrong person).
- Unusual system behaviour (e.g., pop-ups, ransomware notes).
- Any suspected or confirmed data breach, no matter how small.
IV. Mobile & Personal Device Security: Managing a Modern Workforce
These rules manage the risks associated with using mobile and personal devices for work.
23. Mandatory Passcodes/Biometrics
All mobile devices used to access company data must be secured with a minimum 6-digit PIN or strong biometric authentication (FaceID/TouchID). Pattern unlocks or 4-digit PINs are insufficient.
24. Personal Device Security Requirements (BYOD)
Personal devices used to access company data must comply with these standards:
- Supported OS: Devices must run a currently supported OS (e.g., supported iOS or Android versions). Devices stuck on old, unsupported versions must not access company data.
- No Jailbreaking: The device must not be jailbroken or rooted.
- Clean Status: It must not contain illegal software, peer-to-peer (P2P) clients, VPN or hacking tools.
- No Sideloading: Apps must only be installed from official sources (Google Play Store, Apple App Store). “Sideloading” is prohibited.
- Remote Access: Unauthorised third-party remote access software is prohibited.
- Antivirus: It must have an IT-sanctioned antivirus application installed and running correctly. (Exceptions: iPhones and iPads. This is mandatory for all other computers and devices, including Android phones).
- Updates: The operating system and all apps must be kept up-to-date.
25. Approved Applications Only
Only company-approved applications should be used for work-related tasks on any company or personal device.
26. Remote Wipe & Lock Capability
The IT department must have the capability to remotely lock or wipe company data from any device in case of loss or theft.
V. Software and System Management: Maintaining a Healthy IT Ecosystem
Ensuring the smooth operation of company systems requires your cooperation.
27. Adherence to Software Licensing
All software must be properly licensed. Use of pirated software is strictly prohibited.
28. System and Software Update Management
- IT-Managed Updates: You must allow the automatic installation of updates pushed by the IT Department.
- 14-Day Rule: When prompted to restart your computer for updates, you must do so as soon as possible, and certainly within 14 days of the update release. Delaying updates exposes the organisation to critical vulnerabilities.
- User-Initiated Updates: You are prohibited from manually upgrading software without prior IT approval.
- Unsupported Software: Software that is no longer supported by the vendor (“End of Life”) must be removed from the device.
- Specific Instruction – Outlook: At this time, you must not switch to the “New Outlook” toggle. Continue using the standard, IT-deployed version of Microsoft Outlook Classic.
29. Maintenance
- Weekly Reboots: Make sure you restart your PC once per week (ideally on Friday). This means clicking the ‘Start’ icon, ‘Power’ button and then ‘Restart’ – NOT Shutdown.
- Mobile Updates: Mobile device operating system updates must be performed when available or monthly.
30. Working with the IT Department
- Reporting Problems: You must report any IT issues to the helpdesk in a timely manner.
- Security Training: You must participate in all mandatory cyber security awareness training and phishing simulations provided by the company.
- Cooperation with Audits: You are expected to cooperate fully with any IT audits.
VI. Offboarding and Return of Company Assets
The following procedures are mandatory upon the cessation of employment or in the event of company liquidation.
Preservation of Access: It is strictly prohibited for an employee to change passwords, delete accounts, or take any action that would prevent or obstruct the company owner or IT department from accessing any company-related system, account, or data. All access credentials and systems must be left fully intact and accessible.
Immediate Return of Assets: Upon termination of employment for any reason (including resignation), all company equipment, data, and assets must be returned to the company immediately.
Disclosure of Company Data: Employees must declare any company data stored on personal devices or in personal accounts. This data must be securely transferred back to the company and/or permanently erased under the guidance of the IT department.
IT & Security Policy Acknowledgement
By ticking these boxes, I confirm that I have read, understood, and agree to comply with the following key points of the Company IT & Security Policy.
Access & Credentials
[ ] 1. I will use unique 12+ character password for all devices, websites and any other passworded system. Never using the same password twice.
[ ] 2. I will never use an Administrator account for day-to-day emailing or browsing if you have this elevated privilege access.
[ ] 3. I will enable 2FA/MFA on all accounts and never approve a prompt I did not initiate just because it appeared (report it).
[ ] 4. I will never disable 2FA/MFA or delete the authenticator application from my mobile device.
[ ] 5. I agree to store all passwords exclusively in the Windows business MFA secured 365 account using Edge browser or an IT-approved password manager. Anyone with admin access must use an approved password manager only.
[ ] 6. I will never share my passwords or 2FA/MFA codes with anyone. Especially if prompted by a phone call or email with a file/web/doc link.
[ ] 7. I will always lock my screen (Win+L) when stepping away or use auto lock and maintain a Clear Desk.
[ ] 8. I will report any lost/stolen device or suspected data breach to IT immediately.
Online Security & Browsing
[ ] 9. I agree to use only the Microsoft Edge browser for work unless specifically arranged.
[ ] 10. I will not install any browser extensions, unless categorically approved by IT support after security vetting.
[ ] 11. I will not click on paid advertisements in search results or bypass browser security warnings.
[ ] 12. I will treat all emails with suspicion even if they are from known staff members and report all phishing attempts to IT.
[ ] 13. I will verify any email links, attachments, make payment, or change payees details before clicking or actioning them.
[ ] 14. I will use my business direct VPN on public Wi-Fi and ensure any access to work data is done using an approved device.
Software & Acceptable Use
[ ] 15. I understand that company IT resources are for business use and are subject to monitoring.
[ ] 16. I will not use company systems to download copyrighted material or access inappropriate content.
[ ] 17. I will not install any software, VPNs, drivers or alternative browsers without direct approval first.
[ ] 18. I will not use work credentials to sign up for unauthorised third-party websites or services.
[ ] 19. I agree to allow IT to manage updates or allow windows auto updates but will not perform manual updates.
[ ] 20. I will restart my computer ever 7 days and allow critical updates as they become available.
Data & Device Management
[ ] 21. I will save all critical work files only in approved locations like OneDrive/SharePoint only and not to any external service/device.
[ ] 22. I understand company data must not be shared with unauthorised individuals.
[ ] 23. I will not add another staff members login to a PC without IT first approving and configuring the user.
[ ] 24. I will secure any mobile device used for work with a minimum 6-digit PIN/biometrics.
[ ] 25. I confirm any personal device used for work is on the latest firmware updated OS (all) with IT approved antivirus if using Android.
General Compliance & Offboarding
[ ] 26. I agree that company equipment must not be used by third parties, including family.
[ ] 27. I will cooperate fully with IT audits and attend mandatory security training.
[ ] 28. I agree to return all company assets immediately upon termination of my employment.
[ ] 29. I understand I am forbidden from changing passwords or deleting data to obstruct access.
[ ] 30. I acknowledge that non-compliance can lead to disciplinary and/or legal action.
Policy Acknowledgement and Agreement
By signing below, I acknowledge that I have received, read, and fully understood the terms of the Company IT & Security Policy.
I agree to abide by all the rules, regulations, and guidelines outlined in this document as a condition of my employment and my access to the company’s IT resources, networks, and data.
I understand that my compliance is mandatory and that failure to adhere to this policy may result in disciplinary action, up to and including termination of my employment, and may also lead to legal and/or financial liability.
Employee Name (Printed): ____________________________________________
Employee Signature: ____________________________________________
Date: ____________________________________________
Staff IT Security Basic Training Manual
1. Your Accounts and Passwords
Your login credentials are the keys to the company’s data. Protecting them is your most important responsibility.
- Unique Passwords: Every account must have its own unique password. Never reuse a password from a personal account or another work service.
- Password Strength: Use at least 12 random characters, including a mix of letters, numbers, and symbols.
- Use the Vault: Use the approved password manager (Microsoft Edge synced to your 365 profile or IT-sanctioned tools like ProtonPass) to store and generate passwords. Never write them on sticky notes.
- Multi-Factor Authentication (MFA): This is mandatory. Never disable MFA or delete the authenticator app.
- MFA Fatigue Warning: If you get a notification to approve a login that you didn’t initiate, Deny it immediately and report it to IT.
2. Emails and Avoiding Scams
Cybercriminals often use “phishing” emails to trick you into giving up information or transferring money.
- Verify Financial Requests: If you receive an email asking for a money transfer, gift cards, or a change in bank details—even if it looks like it’s from the CEO—you must verify it verbally. Call them on a trusted number or use the Signal app.
- Think Before You Click: Treat every link and attachment with caution. If an email asks you to “log in” to view a file, it is likely a scam.
- Search Safely: Only use the Microsoft Edge browser with Google as the search engine. Never click on “Sponsored” or “Ad” links at the top of search results, as these can lead to fake websites.
3. Looking After Your Devices
Whether you are in the office, at home, or on the road, your hardware must stay secure.
- The “Lock” Habit: Always lock your computer when stepping away (Press Windows Key + L).
- Physical Safety: Never leave devices visible in a car. If they must be left in a vehicle, lock them in the boot (trunk).
- Reporting Loss: If a device is lost or stolen, you must report it to IT within 2 hours so it can be remotely wiped to protect company data.
- Public Wi-Fi: Avoid using public Wi-Fi (cafes, trains, etc.) for work. Use a secure mobile hotspot or the company-provided VPN.
4. Where to Save Your Work
Data should never be “orphaned” on a local drive or a personal cloud.
- Approved Storage: Only save work files to OneDrive for Business or SharePoint.
- Prohibited Areas: Never save sensitive company data to personal USB sticks, personal Dropbox/Google Drive accounts, or your computer’s local ‘C:’ drive.
5. Software and Internet Use
- No Unauthorized Software: Do not install any software, browser extensions (except the approved antivirus), or remote support tools without IT approval.
- Monitoring: Remember that company systems and devices are monitored for security and compliance. There should be no expectation of privacy when using company resources.
- Professionalism: All digital communication must be professional. Do not post confidential info or colleague’s details on social media.
6. Maintenance and Updates
Keeping systems updated is a critical defense against hackers.
- Weekly Reboot: Restart your computer at least once a week (ideally every Friday). Use Restart, not just Shutdown.
- The 14-Day Rule: When you see a notification for a system update, install it as soon as possible. Updates must be completed within 14 days of release.
- Outlook: Continue using the “Classic” version of Outlook. Do not switch to the “New Outlook” toggle unless instructed by IT.
7. Personal Devices (BYOD)
If you use your own phone for work (email/Teams), it must meet these standards:
- Security: A minimum 6-digit PIN or biometrics (Face/Touch ID) is required.
- Updates: Your phone must run a currently supported operating system and be kept up to date.
- Apps: Only download apps from official stores (Apple App Store or Google Play).
Summary Checklist for Staff
- [ ] Is my password 12+ characters and unique?
- [ ] Do I have MFA enabled on all accounts?
- [ ] Am I saving all my files to OneDrive/SharePoint?
- [ ] Did I lock my screen before walking away?
- [ ] Did I restart my computer this week?
If you suspect any security issue—no matter how small—contact the IT Department immediately.